Intune (MEM) NCSC Guidelines Automation
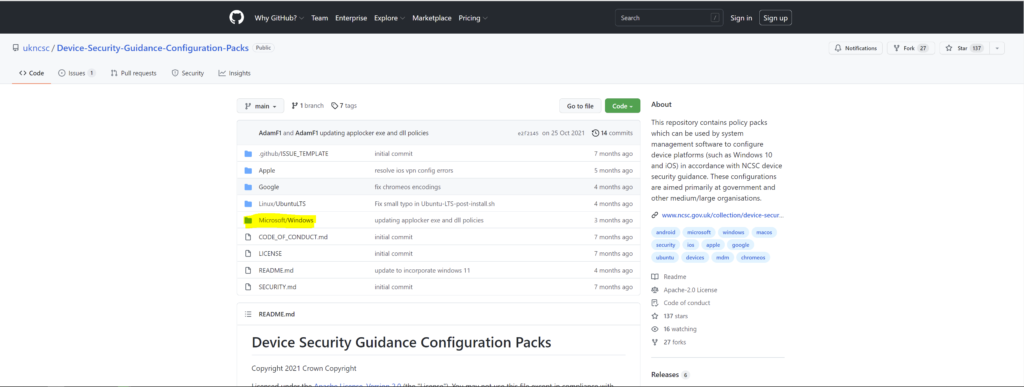
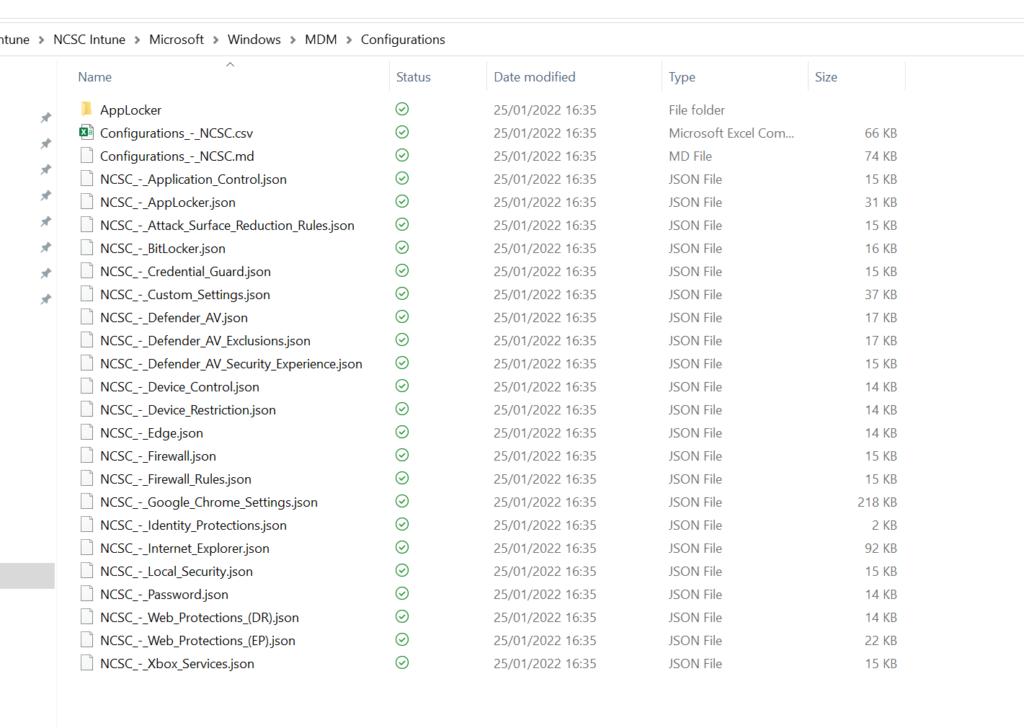
If you are looking to apply NCSC Guidelines in your Intune Configuration profiles then this is the Tutorial for you. All you need to do is Run this PowerShell Script as Admin on your Device and Import JSON files provided by NCSC on their GitHub page.
Run the PowerShell Script you have copied in your PowerShell ISE on Windows 10 as Admin. You will be asked for Authentication. Use your Global Admin account. You will be asked for Password as the Script tries to Install Azure AD Module or Azure AD Preview Module. You will be asked to enter your Password.
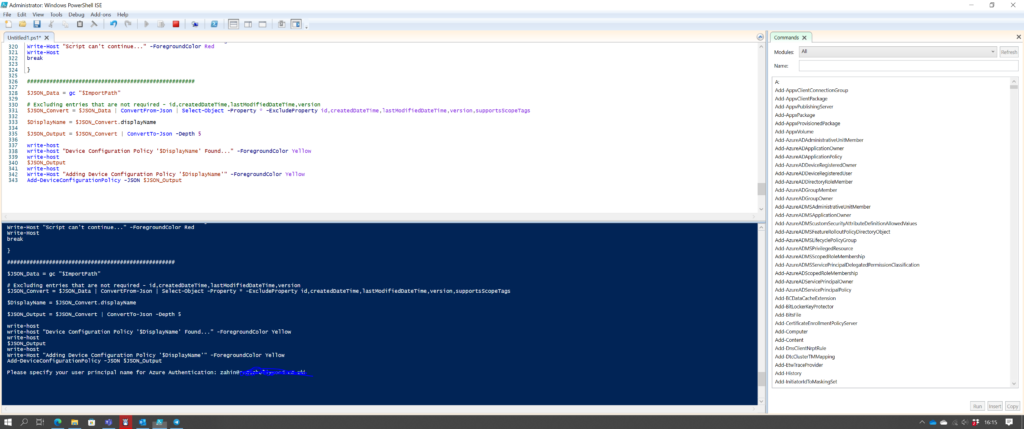
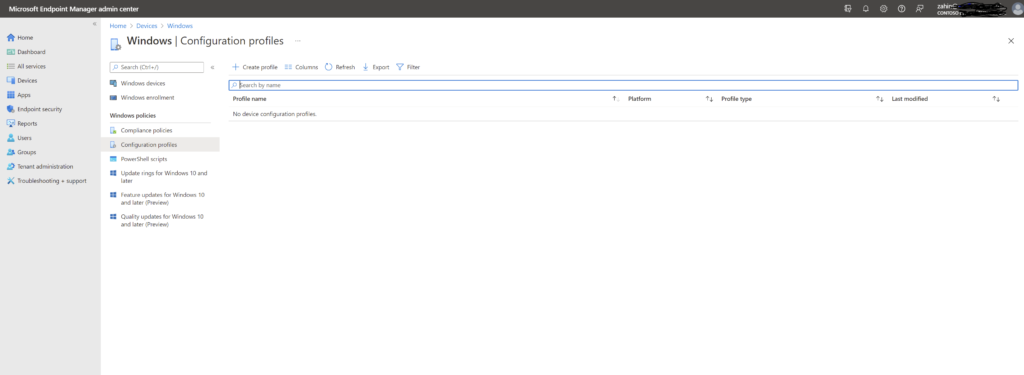
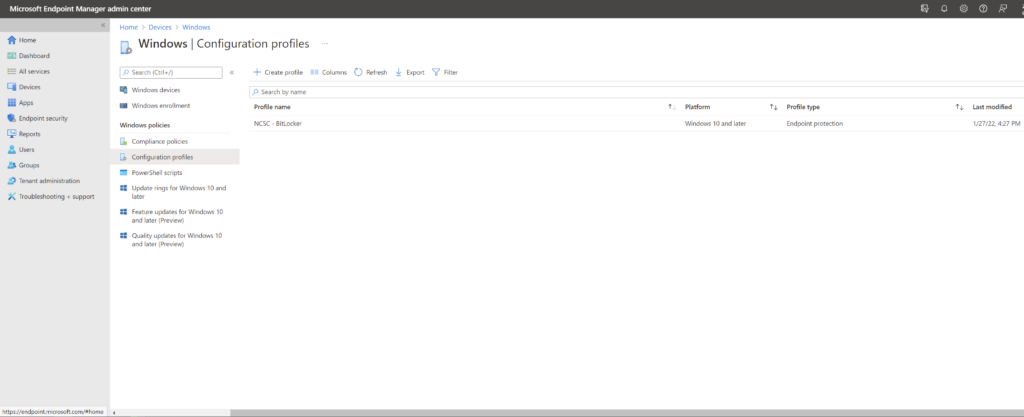
PowerShell Execution will ask you for the location of JSON wile you wish to upload. In my Case, I will start with Bitlocker Config in my brand new Demo Tenant which has no Config Profiles at present. As you can see in below Screenshot.
I am choosing NCSC_-_BitLocker.json file from my Machine. Provide Path and file name in the PowerShell Window.
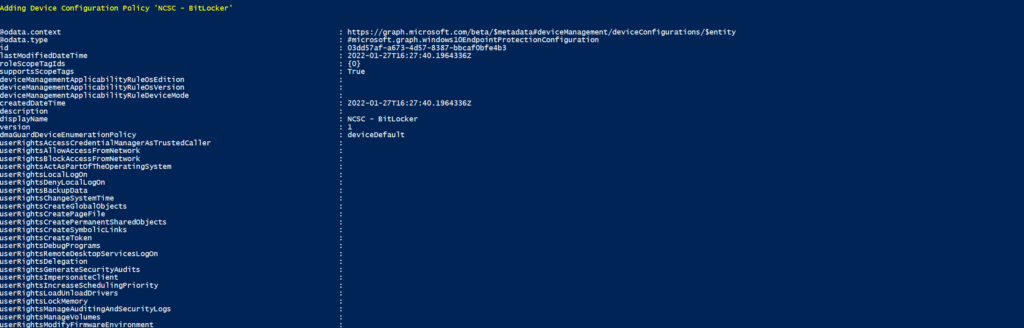
You will see Script running for a couple of Seconds and Profile will be created. Output window will show what was imported and config. I prefer to check the config in Configuration Profile. Below is PowerShell Output Window.
In the Screen below, you can see Configuration profile is now created within Seconds, Instead of you going through NCSC Website and checking Settings and applying them in you Configuration profiles.
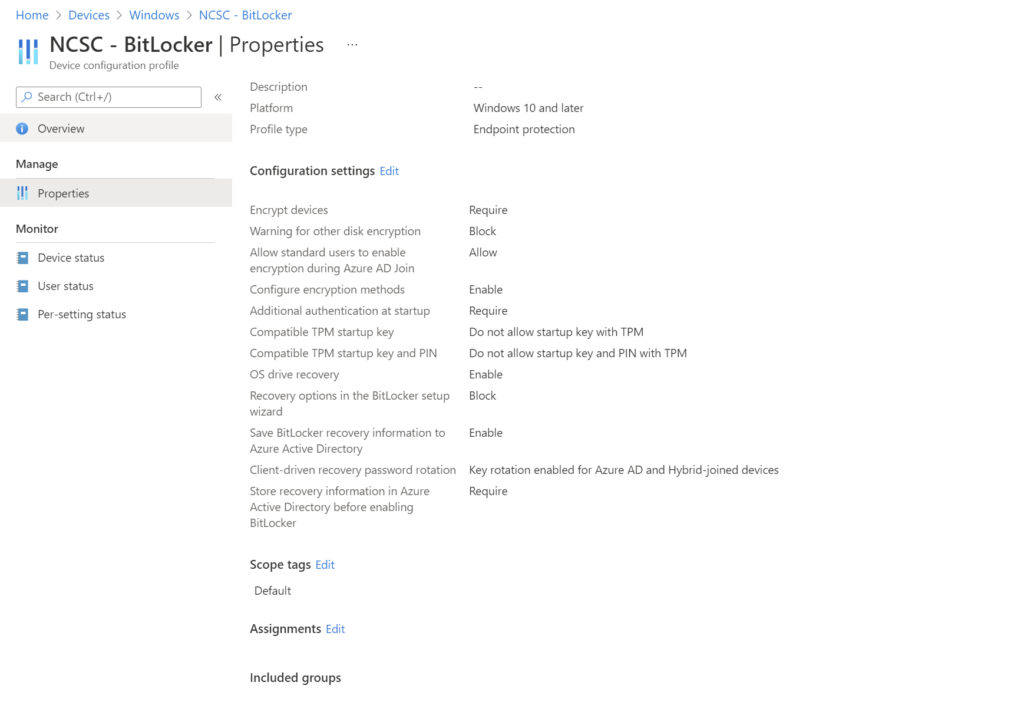
Normally I assign the profile to Autopilot Devices Dynamic Group to all Autpilot Devices.
When this profile was created, Unfortunately default entries were created for Exploit Guard too. Edit the Profile and change all Exploit Guard Entries to Not Configured. It will stop showing with Bitlocker. There is a separate JSON file for Exploit Guard with Defender Policies.
For rest of the of the Configuration Profiles, Run the PowerShell Script again and provide the path of next JSON file in Output Window. Your entire NCSC Device Configuration will finish in 15 minutes or so instead of days doing it manually. Please contact me or comment if you need any help or have questions or suggestions.

Zahin is a Modern Workplace Solutions Architect specialises in End User Compute. He specialises in SCCM, Intune, Azure AD (Entra ID), M365, Windows 10, Windows 11, iOS/iPad OS, Mac OS and other Windows platforms.

